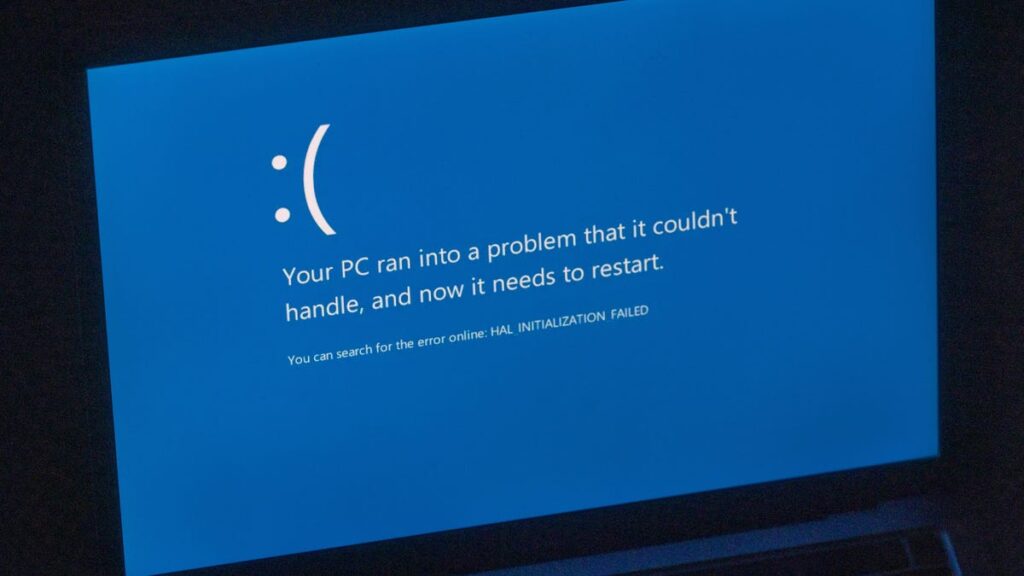
There isn’t a doubt that the great CrowdStrike-Windows meltdown in July 2024 was an financial catastrophe. It was the biggest IT outage in historical past. Its results disrupted banking programs, healthcare networks, and the worldwide air transportation community. Because the post-incident analyses made clear, it was fully preventable.
Additionally: Stop paying for antivirus software. Here’s why you don’t need it
Within the wake of that incident, Microsoft convened a day-long Home windows Endpoint Safety Ecosystem Summit held earlier this week at its Redmond headquarters. The purpose of the closed occasion, which was not open to the press or exterior observers, was to deliver collectively what Microsoft known as “a various group of endpoint safety distributors and authorities officers from the US and Europe to debate methods for bettering resiliency and defending our mutual prospects’ essential infrastructure.”
Did something helpful come out of the session? Who is aware of? Microsoft VP of Enterprise and OS Safety David Weston delivered a wrap-up of the session that was clearly scrubbed by attorneys and communication professionals till all that was left was optimistic company messaging and some obscure hints (“key themes and consensus factors”) of what may occur in Home windows and in endpoint safety merchandise … sometime, however most likely not quickly.
Additionally: Why the NSA advises you to turn off your phone once a week
As that report notes, the roundtable “was not a decision-making assembly … we mentioned the complexities of the trendy safety panorama, acknowledging there are not any easy options.” However one theme that runs by the assembly abstract is a collective realization that the business can not afford one other CrowdStrike incident.
The CrowdStrike incident in July underscored the duty safety distributors must drive each resiliency and agile, adaptive safety. … We face a standard set of challenges in safely rolling out updates to the massive Home windows ecosystem, from deciding tips on how to do measured rollouts with a various set of endpoints to with the ability to pause or rollback if wanted. A core [Safe Deployment Practices] precept is gradual and staged deployment of updates despatched to prospects.
That is a direct critique of CrowdStrike, which brought about the IT outage by rolling out a flawed replace to its whole universe of gadgets slightly than utilizing a staged deployment that would have recognized the issue early and shut off updates to reduce widespread harm.
There’s barely extra coloration within the feedback from assembly contributors that had been appended to the tip of Microsoft’s company weblog publish, like this blast from Ric Smith, Chief Product and Know-how Officer of CrowdStrike competitor SentinelOne:
SentinelOne thanks Microsoft for its management in convening the Home windows Endpoint Safety Ecosystem Summit and we’re totally dedicated to serving to drive its purpose of decreasing the possibility of future occasions just like the one brought on by CrowdStrike. We imagine that transparency is essential and strongly agree with Microsoft that safety corporations should dwell as much as stringent engineering, testing and deployment requirements and comply with software program improvement and deployment greatest practices. We’re proud that we have now adopted the processes that Microsoft has mentioned at present for years and can proceed to take action going ahead. [emphasis added]
Ouch.
What was clearly probably the most energized dialogue, although, revolved round kernel-mode entry to Home windows, a key reason for the CrowdStrike debacle. As I famous just a few months in the past, the scope of the CrowdStrike outage was due largely to the Home windows structure:
Builders of system-level apps for Home windows, together with safety software program, traditionally implement their options utilizing kernel extensions and drivers. As this instance illustrates, defective code operating within the kernel area could cause unrecoverable crashes, whereas code operating in consumer area cannot.
That was once the case with MacOS as properly, however in 2020, with MacOS 11, Apple modified the structure of its flagship OS to strongly discourage the use of kernel extensions. As a substitute, builders are urged to write down system extensions that run in consumer area slightly than on the kernel stage. On MacOS, CrowdStrike uses Apple’s Endpoint Security Framework and says utilizing that design, “Falcon achieves the identical ranges of visibility, detection, and safety completely by way of a consumer area sensor.”
May Microsoft make the identical kind of change for Home windows? Maybe, however doing so would definitely deliver down the wrath of antitrust regulators, particularly in Europe.
Within the broadest attainable phrases, Microsoft’s publish refers to “platform capabilities Microsoft plans to make accessible in Home windows,” with a particular shout-out to safety defaults in Home windows 11 that “allow the platform to supply extra safety capabilities to resolution suppliers exterior of kernel mode. Each our prospects and ecosystem companions have known as on Microsoft to supply further safety capabilities exterior of kernel mode….”
Additionally: Yes, you can upgrade that old PC to Windows 11, even if Microsoft says no. These readers proved it
Not each attendee is thrilled at that concept. Sophos CEO Joe Levy, for instance, politely famous, “We had been more than happy to see Microsoft help lots of Sophos’ suggestions, based mostly on the gathering of architectural and course of improvements we have constructed through the years and current at present on the 30 million Home windows endpoints we shield globally. The summit was an vital and inspiring first step in a journey that can produce incremental enchancment over time….”
What are these suggestions? In an August blog post, Sophos Chief Analysis and Scientific Officer Simon Reed made clear that the corporate considers entry to the Home windows kernel to be basic. “Working in ‘kernel-space’ – probably the most privileged layer of an working system, with direct entry to reminiscence, {hardware}, useful resource administration, and storage – is vitally vital for safety merchandise.” Kernel drivers are “basic,” he wrote, not simply to Sophos merchandise however to “sturdy Home windows endpoint safety, on the whole.”
In a press release that wasn’t attributed to a person, ESET was much more blunt:
ESET helps modifications to the Home windows ecosystem that exhibit measurable enhancements to stability, given that any change should not weaken safety, have an effect on efficiency, or restrict the selection of cybersecurity options. It stays crucial that kernel entry stays an choice to be used by cybersecurity merchandise to permit continued innovation and the flexibility to detect and block future cyberthreats. We stay up for the continued collaboration on this vital initiative. [emphasis added]
And that, finally, is why it is unrealistic to anticipate any sweeping adjustments within the Home windows platform any time quickly. These arguments from Sophos and ESET are clearly shared by leaders at different safety corporations, who worry that limiting entry to the Home windows kernel will give Microsoft’s personal endpoint safety merchandise an important aggressive benefit.
Additionally: 7 password rules to live by in 2024, according to security experts
That is the sort of debate that rapidly will get handed off from engineers to attorneys. Given Microsoft’s historical past with antitrust regulators in Europe and the US, it is more likely to find yourself in courtroom. That is most likely why “authorities officers from the US and Europe” had been invited attendees on the summit, and there isn’t any doubt they had been taking notes.