Russia’s navy intelligence company, the GRU, has long had a reputation as one of many world’s most aggressive practitioners of sabotage, assassination, and cyber warfare, with hackers who take satisfaction in working underneath the identical banner as violent particular forces operators. However one new group inside that company reveals how the GRU could also be intertwining bodily and digital techniques extra tightly than ever earlier than: a hacking staff, which has emerged from the identical unit accountable for Russia’s most infamous bodily techniques, together with poisonings, tried coups, and bombings inside Western international locations.
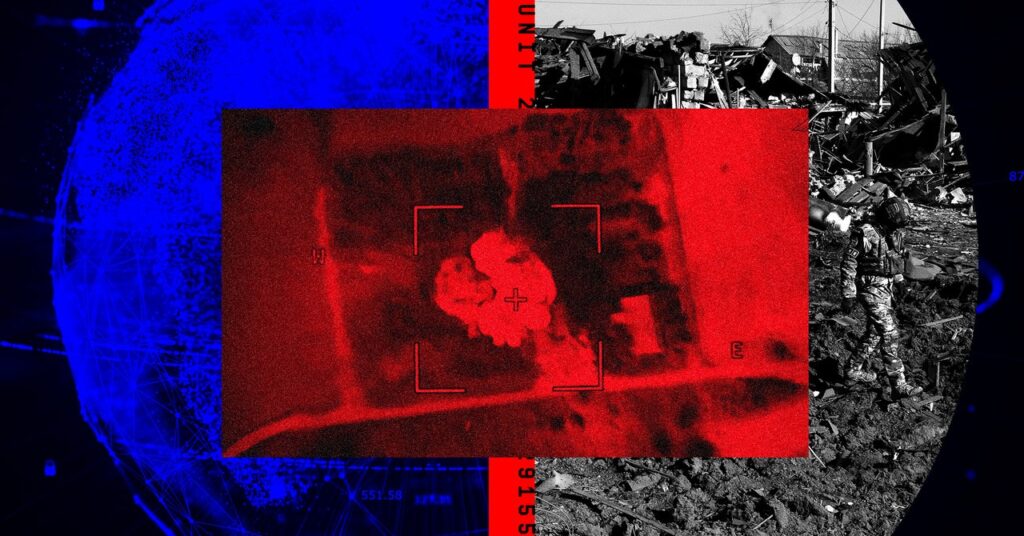
A broad group of Western intelligence companies on Thursday revealed {that a} hacker group generally known as Cadet Blizzard, Bleeding Bear, or Greyscale—one which has launched a number of hacking operations focusing on Ukraine, the US, and different international locations in Europe, Asia, and Latin America—is in reality a part of the GRU’s Unit 29155, the division of the spy company identified for its brazen acts of bodily sabotage and politically motivated homicide. That unit has been tied up to now, for example, to the tried poisoning of GRU defector Sergei Skripal with the Novichok nerve agent within the UK, which led to the loss of life of two bystanders, in addition to one other assassination plot in Bulgaria, the explosion of an arms depot within the Czech Republic, and a failed coup try in Montenegro.
Now that notorious part of the GRU seems to have developed its personal lively staff of cyber warfare operators—distinct from these inside different GRU models comparable to Unit 26165, broadly generally known as Fancy Bear or APT28, and Unit 74455, the cyberattack-focused staff generally known as Sandworm. Since 2022, GRU Unit 29155’s extra not too long ago recruited hackers have taken the lead on cyber operations, together with with the data-destroying wiper malware generally known as Whispergate, which hit Ukrainian organizations on the eve of Russia’s February 2022 invasion, in addition to the defacement of Ukrainian authorities web sites and the theft and leak of knowledge from them underneath a pretend “hacktivist” persona generally known as Free Civilian.
Cadet Blizzard’s identification as part of GRU Unit 29155 reveals how the company is additional blurring the road between bodily and cyber techniques in its strategy to hybrid warfare, in keeping with one in every of a number of Western intelligence company officers whom WIRED interviewed on situation of anonymity as a result of they weren’t licensed to talk utilizing their names. “Particular forces don’t usually arrange a cyber unit that mirrors their bodily actions,” one official says. “This can be a closely bodily working unit, tasked with the extra ugly acts that the GRU is concerned. I discover it very stunning that this unit that does very hands-on stuff is now doing cyber issues from behind a keyboard.”
Beyonds its beforehand identified operations towards Ukraine, Western intelligence company officers inform WIRED that the group has additionally focused all kinds of organizations in North America, Japanese and Central Europe, Central Asia, and Latin America, comparable to transportation and well being care sectors, authorities companies, and “essential infrastructure” together with “power” infrastructure, although the officers declined to supply extra particular data. The officers instructed WIRED that in some circumstances, the 29155 hackers gave the impression to be making ready for extra disruptive cyberattacks akin to Whispergate, however did not have affirmation that any such assaults had really taken place. The US Division of State in June individually revealed that the identical GRU hackers who carried out Whispergate additionally sought to search out hackable vulnerabilities in US essential infrastructure targets, “significantly the power, authorities, and aerospace sectors.”
In lots of circumstances, the 29155 hackers’ intention gave the impression to be navy espionage, in keeping with Western intelligence company officers. In a Central European nation, for example, they are saying the group breached a railway company to spy on prepare shipments of provides to Ukraine. In Ukraine itself, they are saying, the hackers compromised client surveillance cameras, maybe to achieve visibility on motion of Ukrainian troops or weapons. Ukrainian officers have beforehand warned that Russia has used that tactic to focus on missile strikes, although the intelligence officers who spoke to WIRED did not have proof that 29155’s operations particularly had been used for that missile focusing on.